Executive Summary
This post describes how to install Microsoft Virtual PC 2007, followed by a detailed walk-through of how to create a virtual machine image of a fresh Windows 7 installation using Virtual PC 2007.
In this post I concentrate on creating a Virtual PC image for Windows 7, but the steps for the other operating systems are similar.
Note this post deals with concerns for Developers. This post does not cover use of (related) virtualization techniques which are very popular today on the server-side.
Why Use Virtual Machines?
There are several reasons to use a Virtual PC-managed virtual machine for development:
You don’t want to install Pre-Release software (like a CTP – Community Technology Preview, which means “very rough”) or beta software directly on your development machine. A virtual machine environment makes it easy to manage these without risking your real machine.
You want to experiment. You may want to try out some testing with 4 GB or RAM, then maybe with 1/2 GB or RAM – so you know what to expect. Or you to keep testing something that changes your machine – and need to “start from scratch” frequently.
You want to run multiple operating systems. You may want to run Windows 7 to make sure your apps run fine on it – but you also don’t want to give up XP quite yet. You can run Windows 7 within a Windows XP host.
You want to set up a machine configuration and reuse it. You go through a lot of trouble to get your configuration “just so” and now want to share that with colleagues – or with yourself (on your home machine).
Are there other Virtualization options?
If you are a developer running XP -or- are running Win 7 on hardware that does not support hardware virtualization, Virtual PC 2007 is very likely what you want.
If you are running Windows 7, you can look into Virtual PC (sometimes seen as Virtual PC 7) (which includes XP Mode). Unlike Virtual PC 2007 which will work regardless of whether you have hardware virtualization, Virtual PC will work ONLY WHEN your computer supports hardware virtualization. Does my PC support hardware virtualization (or XP Mode)?
Unlike Virtual PC 2007, Virtual PC is for Windows 7 will not work on XP (but will work on the Windows 7 beta, sometimes known as Vista :-).
Only one of Virtual PC -or- Virtual PC 2007 can be installed concurrently on any given machine.
From Microsoft, other vendors, and open source, there are other sources of virtualization technology, and some might even be compatible with Virtual PC or VHD. [Did you know VHD format is an open standard?]. Though, consider that Virtual PC 2007 does not cost anything beyond the Windows license you (presumably) already have. Microsoft has many virtualization solutions, some with different purposes, such as App-V which is more for enterprise roll-out of apps (get it? App-V) to minimize incompatibilities due to other apps or environmental changes.
For developers, let’s assume (for reasons stated above in prior section) that you want a parallel universe to run other software within – safely – like an early beta… Virtual Machine images make these scenarios possible and easy! Let’s get down to business and walk through how to install & configure these virtual images.
Ready to Get Started?
Enable Hardware Virtualization in your Computer
The newer your PC, the more likely it is that it supports hardware acceleration for Virtualization. If you have this, you want to enable it for better performance. You may need to enable it in your BIOS. Unfortunately, the specific instructions will vary by computer manufacturer, so you’ll need to search the web for steps to enable Hardware Assisted Virtualization.
Installing Virtual PC 2007
Visit the download page for Microsoft Virtual PC 2007 download page for Microsoft Virtual PC 2007 sp1 and then select the appropriate version for your system (that is, 32- or 64-bit version).

Once downloaded, install it.

If you already have an earlier version of Virtual PC installed, you will likely see this self-explanatory message to uninstall the older version. If you are upgrading to Virtual PC 2007 sp1 from Virtual PC 2007, the installer will handle it for you.

Go to your trusty Add or Remove Programs applet and remove any remnants of old Virtual PC installs and proceed.
You can run Virtual PC 2007 and look in Help > About to see which version you are running. Version “Microsoft Virtual PC 6.0.192.0” is Virtual PC 2007 sp1, which is the one expected by the rest of this post.
Installing Microsoft Virtual PC 2007
Run Virtual PC 2007 installer …



.. fill in your own info here, of course.

I kept the default installation location and let it rip. It completed around 2 minutes later.
NOW GET DOWN TO BUSINESS!
Create fresh Windows 7 virtual machine environment using Microsoft Virtual PC 2007
Download Your Windows 7 ISO Image
In order to install Windows 7, you need a copy of Windows 7. This could be a retail version of Windows 7 (from a DVD), but let’s make the assumption here that since you are a developer, you will be using a download image from MSDN that comes down as an ISO file, such as en_windows_7_professional_x86_dvd_x15-65804.iso. Note that you will need to install a 32-bit operating system to run under Virtual PC 2007. Log in to your MSDN account and select an appropriate version of Windows 7 to download, download it, and also be sure to copy the Activation Key (if applicable).
Run Upgrade Advisor
You may wish to run the Windows 7 Upgrade Advisor on your machine to make sure Windows 7 will be happy (as of this writing, the upgrade advisor tool is in beta). Assuming that goes well..
Run Virtual PC 2007
Run Microsoft Virtual PC 2007. From the opening screen, click the “New…” button:

The wizard will start. Click the “Next >” button:


Select “Create a virtual machine” and click “Next >” button…
Give your new Virtual Machine an appropriate name:

I also changed my location:

Select “Other” as Operating system and click “Next >” …

The recommended RAM will likely not be sufficient, so click “Adjusting the RAM” option:

How much memory is right? Considering Windows 7 system requirements (which call for at least 1 GB in the 32-bit version) and Visual Studio 2010 (beta 1) system requirements (which also calls for 1 GB (though not an additional 1 GB), you will hopefully be able to allocate at least 1 GB. I have 3 GB on my host machine, so I allocated 1.5 GB (1024 MB + 512 MB = 1536 MB). These values can also be tweaked later using Virtual PC.

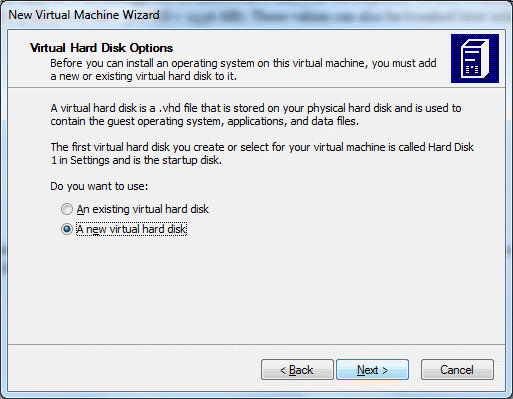
I chose to create a new virtual disk:
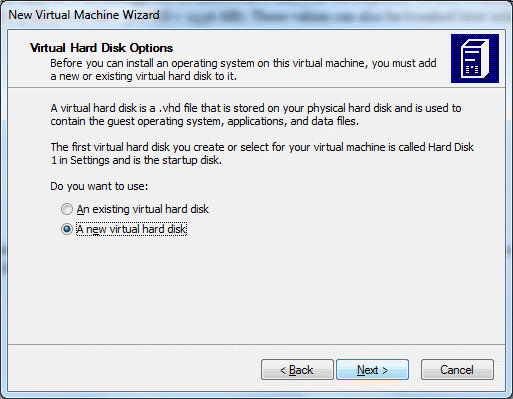
For disk space, you have another set of decisions – Windows 7 wants 15 GB, Visual Studio 2010 wants 3 GB, so I rounded up to a nice even 18.5 GB (since I don’t have an abundance of space here):

Click “Next >” and you are almost done with this step.

Click “Finish” and now we are in business within Virtual PC:

Click on “Azure Dev” (or whatever you called your image) and click “Start” button to proceed:
If you have trouble starting your virtual machine due to not enough memory available, as in the following message, you either need to adjust its memory requirements of free up some memory.
You might consider throttling back your Anti-Virus software which could be a big consumer of memory (I disabled the on-the-fly file-system protection). Also, of course, close all unnecessary processes. The long-term solution is to buy a 64-bit machine with oodles of memory and be happy with that.
Once you have enough memory available, you will see the virtual machine complain very soon as it craps out after spinning up and thinking for a couple of minutes:

This is expected. You still need to install Windows 7 to move this along. To do this, make sure you have a ready-to-go image of Windows 7 as an ISO file (as you might download from MSDN) or physical media. You have two menu options, one for each of these cases:

In my case, I selected “Capture ISO Image…” and installed from there. Note that you navigate your host file-system for the ISO image to capture – not the file-system on your virtual machine, since that does not yet exist.

Click “Open” and notice how the CD menu on the virtual machine has been updated:

Now you can reboot your virtual machine to let the installation on the captured ISO image run (as if it was auto-starting to install on a physical machine). To reboot, choose Reset from the Action menu:

You will be warned:

But since you don’t have any unsaved changes to worry about, select the Reset button and proceed with the reset. (You have saved some information, you may be thinking, like memory and hard disk configuration; but that is all metadata about your image – not changes within the virtual machine itself – so there is no problem here.)
The reset begins…

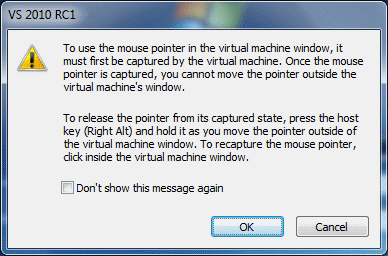
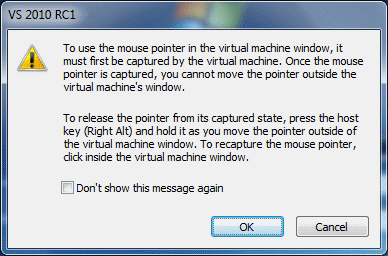
Here is a warning which we will come back to. Dismiss this for now:

The system will chug and chug for a looong time – mine took around two hours to run (the good news is I let this run while I was watching the New England Patriots game this Sunday; the bad news is the Patriots fell to the Jets):

You will then proceed to install Windows 7 … mostly you will be just moving along without much fanfare, though you will need to name your “computer”, come up with a username (and optionally a password), and will need your Activation Key for Windows 7. Here is a good guide for installing Windows 7 on Virtual PC 2007. (And another.)
Don’t that forget the magic key/mouse combo to un-capture your mouse from the Virtual Machine is Right-Alt while dragging the mouse!!

After you get Windows 7 all configured, you probably still want to come back and install some updates:


But that’s the end of the detailed tour. You should now have a usable baseline virtual machine image that you can reuse, share, play with, etc. Make sure you create a back-up copy! And have a look at the features which allow you to manage roll-backs.
Good luck!